Learn to Prevent code tampering in Mobile apps, in mobile CI/CD with a Data-Driven DevSecOps™ build system.
Tampering involves the modification of a mobile app (either the compiled app or the running process), or the mobile app’s environment, thereby affecting the app behavior. For example, an app might not run on your rooted test device, thus preventing any option to run some of your tests.
Tamper prevention protects your app against unwanted changes, mods, and hacks – all without adding development work or time to your release cycles. This is done by sealing your app and actively detecting modifications during initialization and at multiple other points during run-time (whenever the app is being used).
Mobile Anti-Tampering protects against the following static and dynamic modifications to the application:
To use Appdome’s mobile app security build system to Prevent code tampering , you’ll need:
On Appdome, follow these 3 simple steps to create self-defending Mobile Apps that Prevent code tampering without an SDK or gateway:
Prevent Code Tampering Compatible With: Obj-C, Java, JS, C#, C++, Swift, Kotlin, Flutter, React Native, Unity, Xamarin, and more
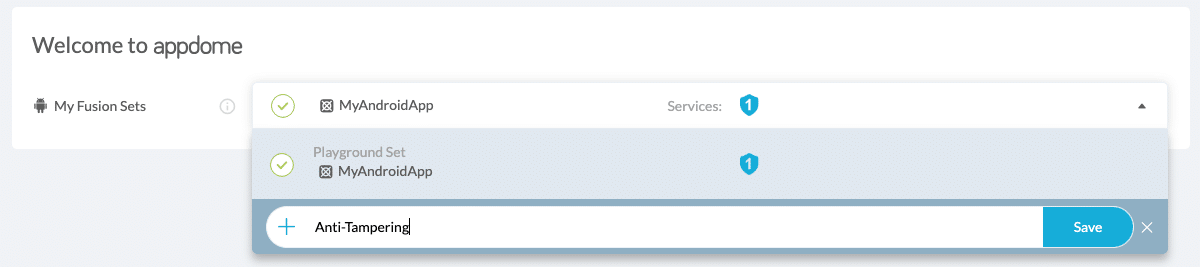
Create and name the Fusion Set (security template) that will contain the Prevent Code Tampering feature as shown below:
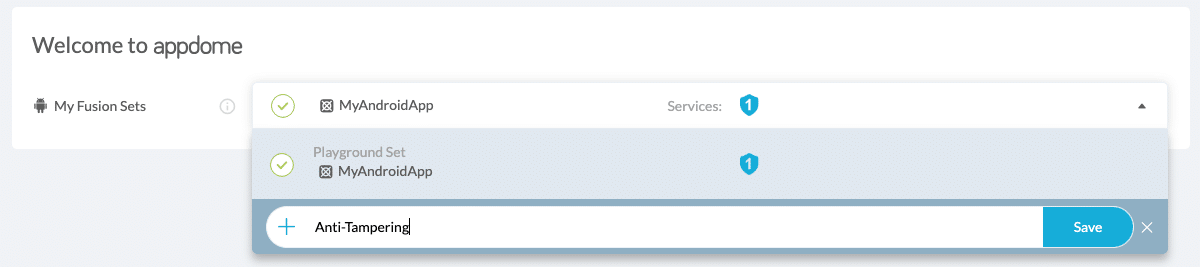
Figure 1: Fusion Set that will contain the Prevent Code Tampering feature
Note: Naming the Fusion Set to correspond to the protection(s) selected is for illustration purposes only (not required).
Follow the steps in Sections 2.2.1-2.2.2 of this article, Building the Prevent Code Tampering feature via Appdome Console, to add the Prevent Code Tampering feature to this Fusion Set.
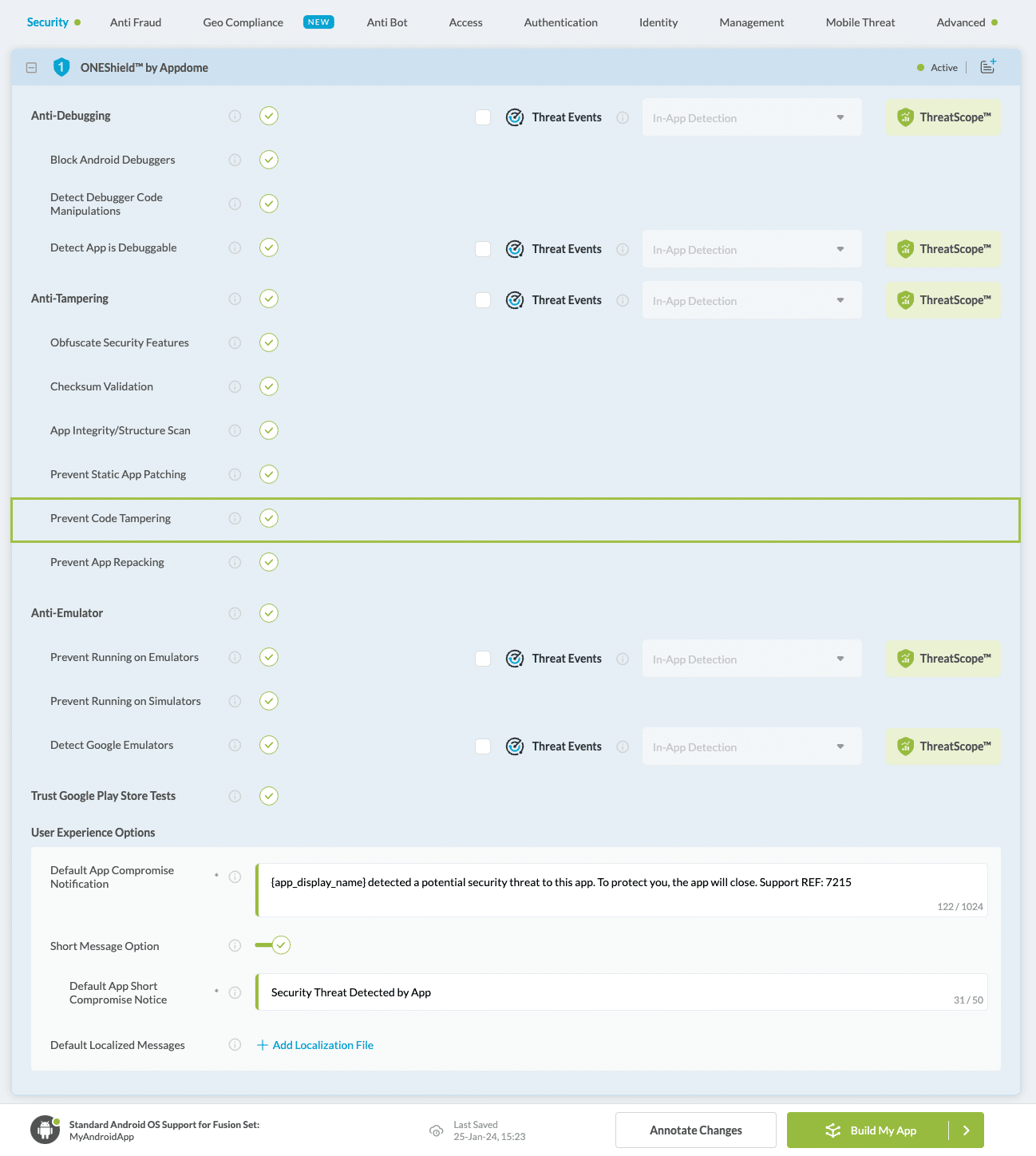
Open the Fusion Set Detail Summary by clicking the “. ” symbol on the far-right corner of the Fusion Set. Copy the Fusion Set ID from the Fusion Set Detail Summary (as shown below):
Figure 2: Fusion Set Detail Summary
Note: Annotating the Fusion Set to identify the protection(s) selected is optional only (not mandatory).
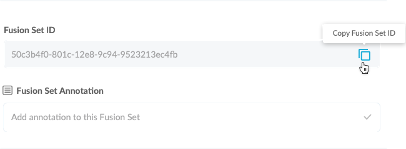
Like all other options in ONEShield™, Prevent Code Tampering is turned on by default, as shown below: Figure 3: Prevent Code Tampering option
Note: The App Compromise Notification contains an easy to follow default remediation path for the mobile app end user. You can customize this message as required to achieve brand specific support, workflow or other messaging.
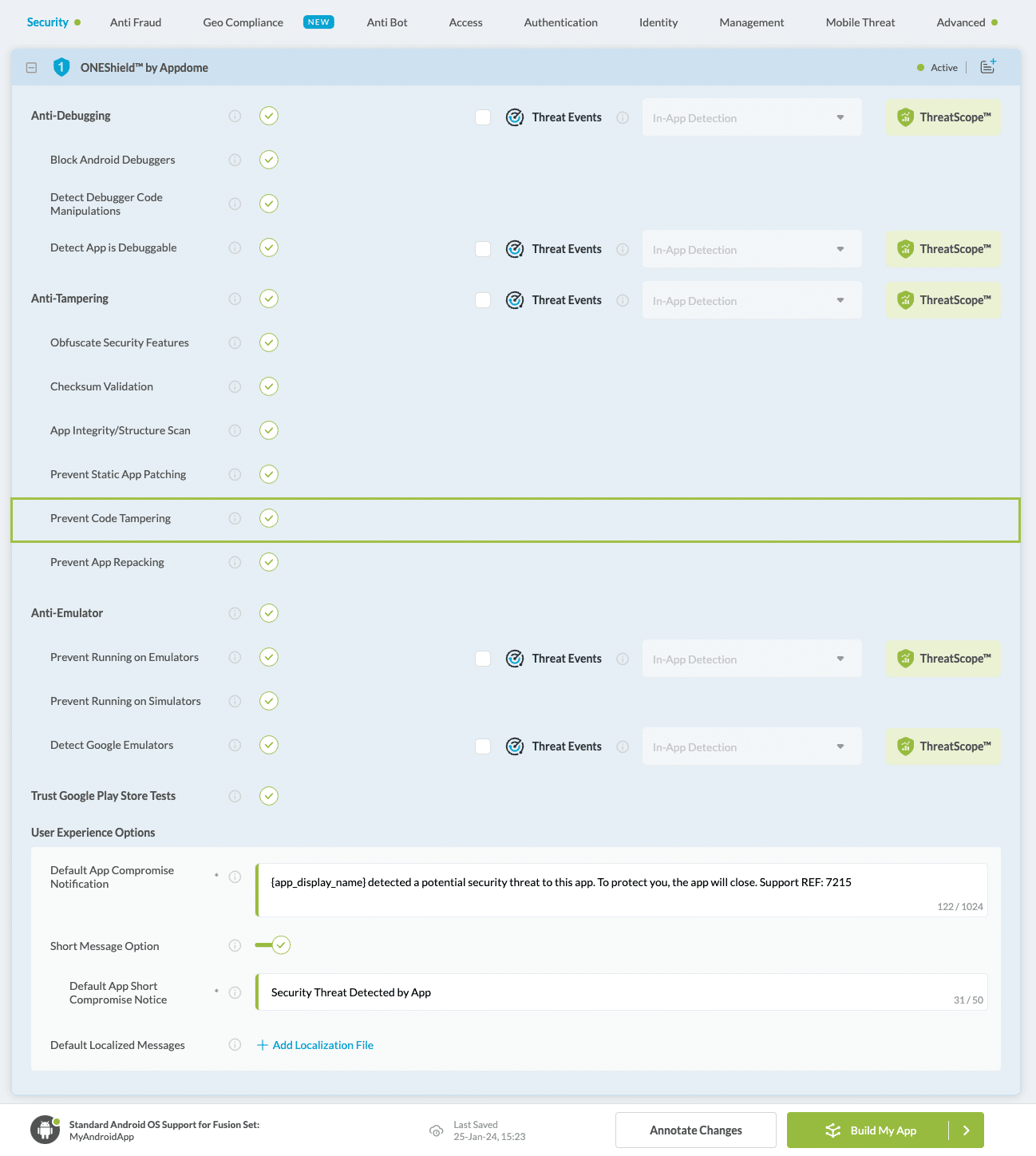
How: Toggle (turn ON) Prevent Code Tampering, as shown below.
If needed, Customize the Threat Notification to be displayed to the mobile end-user in a standard OS dialog notification when Appdome Prevents code tampering.
Figure 3: Prevent code tampering option
Note: The App Compromise Notification contains an easy to follow default remediation path for the mobile app end user. You can customize this message as required to achieve brand specific support, workflow or other messaging.
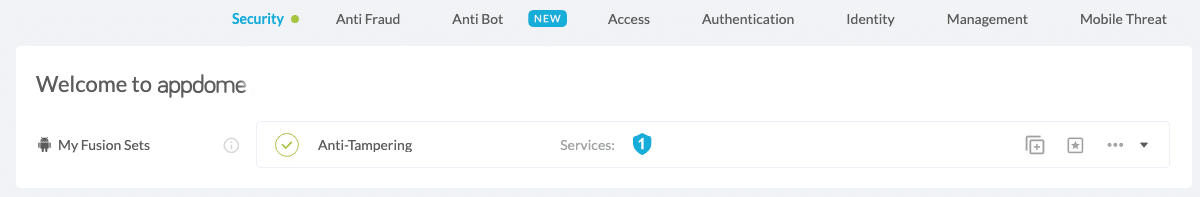
When you select the Prevent Code Tampering you'll notice that your Fusion Set you created in step 2.1.1 now bears the icon of the protection category that contains Prevent Code Tampering
Figure 4: Fusion Set that displays the newly added Prevent Code Tampering protection Checksum Validation App Integrity/Structure Scan Prevent Static App Patching Prevent Code Tampering Prevent App Repacking Click Build My App at the bottom of the Build Workflow (shown in Figure 3). Congratulations! The Prevent Code Tampering protection is now added to the mobile app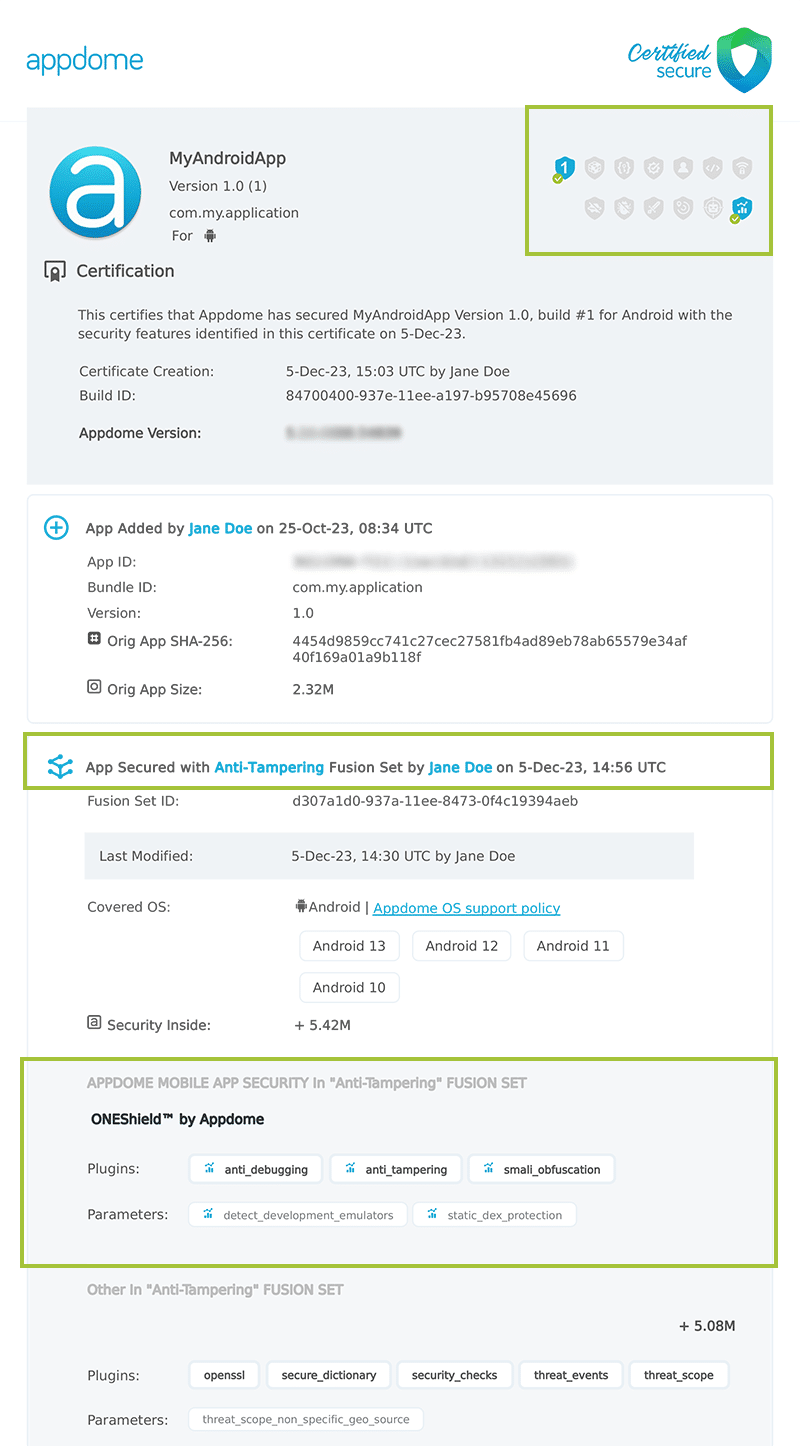
After building Prevent Code Tampering, Appdome generates a Certified Secure™ certificate to guarantee that the Prevent Code Tampering protection has been added and is protecting the app. To verify that the Prevent Code Tampering protection has been added to the mobile app, locate the protection in the Certified Secure™ certificate as shown below: Figure 5: Certified Secure™ certificate Each Certified Secure™ certificate provides DevOps and DevSecOps organizations the entire workflow summary, audit trail of each build, and proof of protection that Prevent Code Tampering has been added to each Mobile app. Certified Secure provides instant and in-line DevSecOps compliance certification that Prevent Code Tampering and other mobile app security features are in each build of the mobile app
Appdome Threat-Events™ provides consumable in-app mobile app attack intelligence and defense control when code tampering is detected. To consume and use Threat-Events™ for code tampering in Mobile Apps, use AddObserverForName in Notification Center, and the code samples for Threat-Events™ for code tampering shown below.
The specifications and options for Threat-Events™ for code tampering are:
| Threat-Event Context Keys | |
|---|---|
| message | Message displayed for the user on event |
| failSafeEnforce | Timed enforcement against the identified threat |
| externalID | The external ID of the event which can be listened via Threat Events |
| osVersion | OS version of the current device |
| deviceModel | Current device model |
| deviceManufacturer | The manufacturer of the current device |
| fusedAppToken | The task ID of the Appdome fusion of the currently running app |
| kernelInfo | Info about the kernel: system name, node name, release, version and machine. |
| carrierPlmn | PLMN of the device. Only available for Android devices. |
| deviceID | Current device ID |
| reasonCode | Reason code of the occurred event |
| buildDate | Appdome fusion date of the current application |
| devicePlatform | OS name of the current device |
| carrierName | Carrier name of the current device. Only available for Android. |
| updatedOSVersion | Is the OS version up to date |
| deviceBrand | Brand of the device |
| deviceBoard | Board of the device |
| buildUser | Build user |
| buildHost | Build host |
| sdkVersion | Sdk version |
| timeZone | Time zone |
| deviceFaceDown | Is the device face down |
| locationLong | Location longitude conditioned by location permission |
| locationLat | Location latitude conditioned by location permission |
| locationState | Location state conditioned by location permission |
| wifiSsid | Wifi SSID |
| wifiSsidPermissionStatus | Wifi SSID permission status |
With Threat-Events™ enabled (turned ON), Mobile developers can get detailed attack intelligence and granular defense control in Mobile applications and create amazing user experiences for all mobile end users when code tampering is detected.
The following is a code sample for native Mobile apps, which uses all values in the specification above for Prevent Code Tampering:
Java Kotlin Xamarin/MAUI Android Swift Objective-C Xamarin/MAUI iOS React Native Cordova Flutter IntentFilter intentFilter = new IntentFilter(); intentFilter.addAction(""); BroadcastReceiver threatEventReceiver = new BroadcastReceiver() < @Override public void onReceive(Context context, Intent intent) < String message = intent.getStringExtra("message"); // Message shown to the user String reasonData = intent.getStringExtra("reasonData"); // Threat detection cause String reasonCode = intent.getStringExtra("reasonCode"); // Event reason code String currentThreatEventScore = intent.getStringExtra("currentThreatEventScore"); // Current threat event score String threatEventsScore = intent.getStringExtra("threatEventsScore"); // Total threat events score String variable = intent.getStringExtra(""); // Any other event specific context key // Your logic goes here (Send data to Splunk/Dynatrace/Show Popup. ) > >; if (Build.VERSION.SDK_INT >= Build.VERSION_CODES.TIRAMISU) < registerReceiver(threatEventReceiver, intentFilter, Context.RECEIVER_NOT_EXPORTED); >else